Managing File Shares
Discover, classify, and control your unstructured file share data
Manage Data Growth
One of the biggest problems plaguing corporations today is the explosive growth of data. File share grow on average 63% every year and 80% of that data is unstructured. File shares have become the new digital dumping ground and pose one of the biggest potential risks to an organization through a lack of control and visibility. Heureka changes the game by automatically indexing and classifying file share data.
Easy-to-install, file-share specific
indexing engine
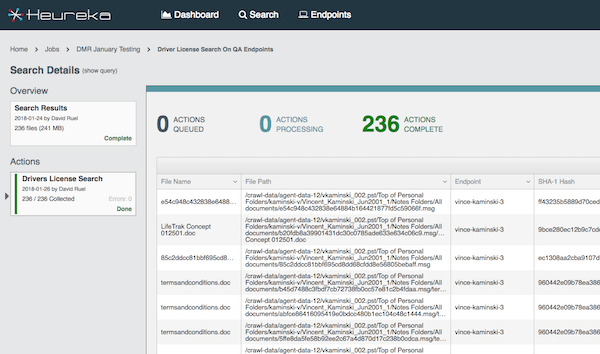
Auto-classification engine identifies PII information including Social Security Numbers, Credit Card Numbers and Bank Routing information.
Install on Linux, Windows
and macOS
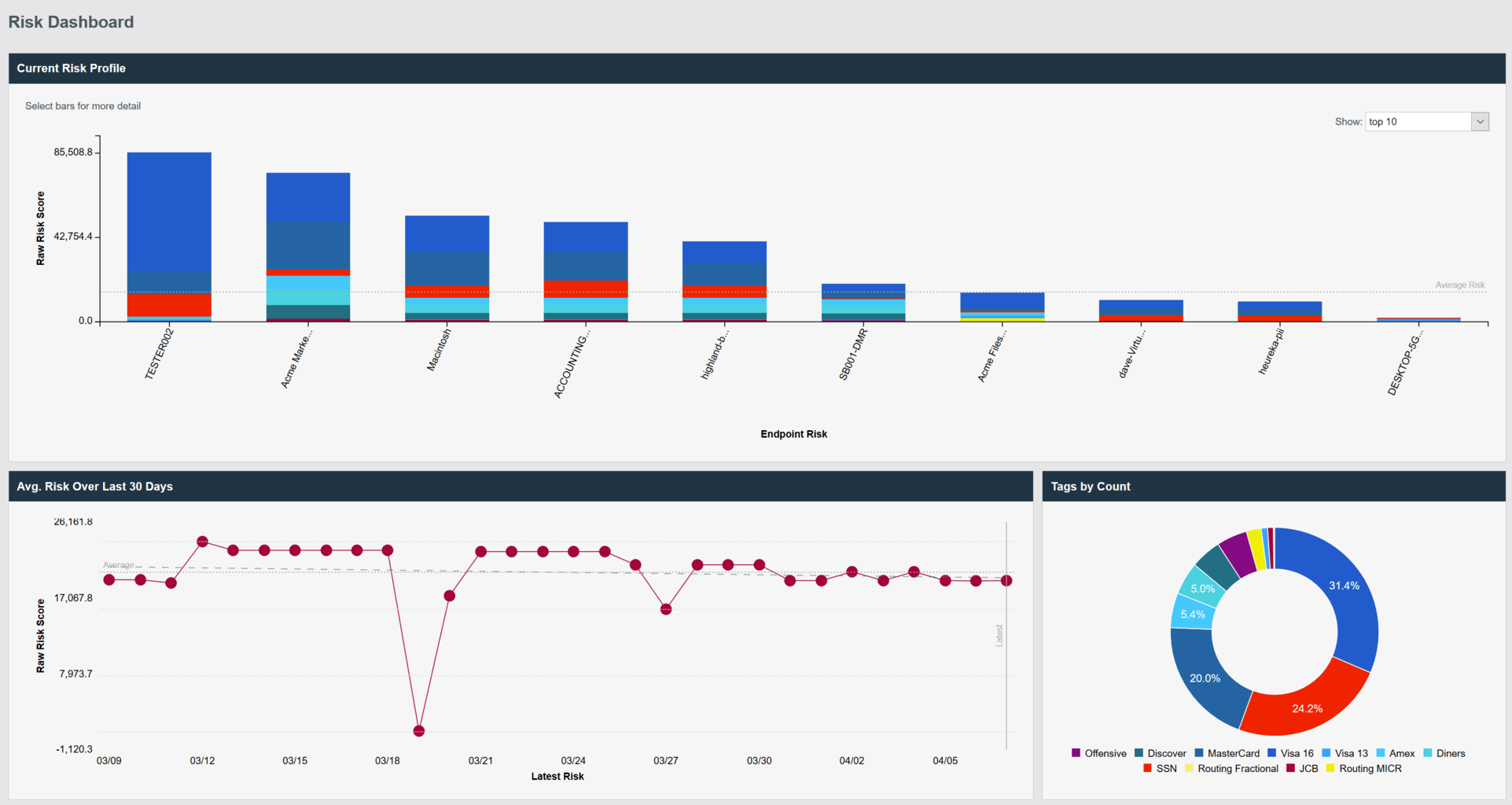
Broad array of search tools including keywords, Boolean queries, file names, file hash values, date filtering, and regular expressions
Scheduled searching allows automated searches to be performed “hands off”
Manage false positives with combination classification tags and keywords or Boolean values
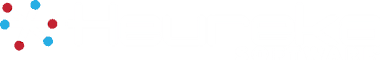
Risk dashboard provides instant view of riskiest file shares or endpoint compute
Remediation tools for managing risk include collect, quarantine and delete
Heureka For File Shares
Tools for managing file shares are often cumbersome and incomplete and offer little more than cursory information about the data. Because of time and resource constraints, most organizations simply continue to add drive space instead of attempting to solve the real problem around content analysis and elimination of ROT (Redundant, Obsolete, Trivial) data.
Find and Protect Your Data Now
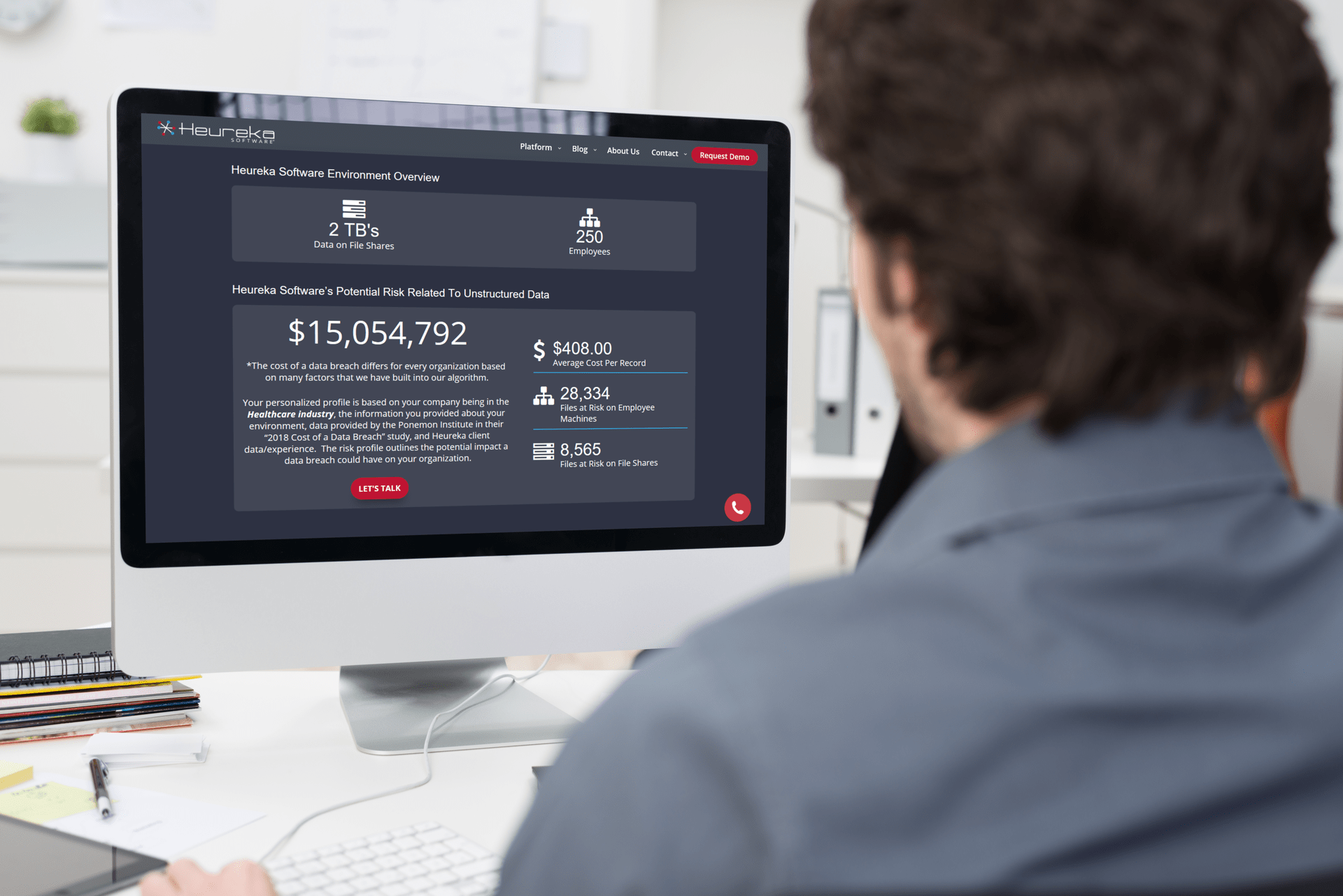
Data breaches continue to be an almost daily news story with PII and PHI information being exposed, leaked or stolen and sold on the dark web. Record fines on corporations continue to pile up as privacy regulation and laws continue to be written and passed across the globe.
The window of opportunity to manage your unstructured data continues to close and according to the Identity Theft Resource Center, exposed Consumer PII records have increased 126% since 2017.
The time to begin managing your file share data is right now and Heureka Software provides the perfect platform to gain knowledge and control over your unstructured file share data.
Heureka Provides Real ROI
In today’s data-rich environment, information security is becoming more vital to an organization. Laws and regulations such as GDPR or CCPA continue to drive organizations toward a data-focused security posture. The days of not knowing where critical and sensitive data reside within an organization are disappearing.
Heureka provides true ROI by identifying risk in areas of the organization that previously had zero visibility along with tools to remediate issues including secure file collection, defensible deletion or file quarantining all from the same platform.
Heureka serves multiple business segments including financial investment firms, higher education, insurance companies, city and county governments and law and litigation support companies. Heureka provides rapid value — often within the first 24-hours — as our automatic index and classification engines begin illuminating potential risk throughout the environment.
Real-world examples of how Heureka is helping our clients identify and remediate risk on their file shares and endpoints.
The Struggle To Identify And Protect Risky Information Is Real
IT departments, CISO’s, CTO’s and data protection officers are being asked to do more with less. Heureka Software provides a single platform to service multiple areas of your business from governance, risk and compliance to legal and cyber security.
Heureka’s platform is designed to free up valuable time and effort required to find and identify information regardless of where it is in your network. Isn’t it time to take control of your data?
Other Heureka Solutions
Lightening fast, enterprise-wide data searching and classification.
GDPR

Governance & Compliance
Heureka ACT™ FAQs
What Is Heureka's Advanced classification and tagging?
ACT approaches classification and tagging in two ways. First, Heureka’s daily classification engine automatically detects PII such as credit and social security numbers along with bank routing information. Each system then automatically reports risk back to your dashboard and tracks risk trends across 30 days. Second, ACT allows users to add or import classification and tag intelligence and keep that intelligence in sync at all times across all installed systems. A central tag library stores all tag information and provides import tools for intelligence sharing.
How does ACT help in the legal E-Discovery field?
ACT provides a workflow allowing for the application and reuse of tagging decisions created in E-Discovery review platforms. These time consuming and costly decisions are typically lost when a case or matter is closed. Heureka allows users of Relativity®, iConect®, Logikcull® and Zapproved® to import tags back into the ACT library and apply them against files on endpoint computers. Tags are automatically sync’d to all computers and each search will immediately return any new tag intelligence.
How does ACT help with information and privacy professionals?
Heureka provides daily risk intelligence by automating the process of locating and tagging PII information. Each day the Heureka classification engine identifies risky information such as social security and credit card numbers as well as bank routing numbers and offensive terms. All information is reported to a risk dashboard which also tracks risk trends over 30-days. Risk tags are automatically applied by ACT along with a Heureka risk score based on risk type and quantity. Heureka provides a centralized view across the enterprise but more importantly provides the tools necessary to remediate any file-level issue, from any source in the Heureka environment.
How does ACT interact with A.I. and Machine Learning platforms?
Virtually any analytics engine has the capability to interact with Heureka ACT by exporting classification or tag information. Heureka’s centralized ACT library easily imports data in and then applies the intelligence across any matching file in the Heureka installed environment. Heureka’s shared intelligence workflow provides bi-directional tagging transfers and has a RESTful tagging API in which platform intelligence can easily be accessed. Heureka works with platforms such as Ayfie®, Canopy® and Contexture®.